您好,登录后才能下订单哦!
实验目的:
1.VLAN互通
2.VRRP
3.内网PAT访问外网【地址转换成119.1.1.0/29网段】
4.发布Web服务器供外网访问
实验步骤:
配置各个交换机:
SW1:创建vlan1【交换机自带】、vlan2、vlan100
interface GigabitEthernet0/0/1
port link-type access
port def vlan 1
interface GigabitEthernet0/0/12
port link-type trunk
port trunk allow-pass vlan 2 to 4094
interface GigabitEthernet0/0/13
port link-type trunk
port trunk allow-pass vlan 2 to 4094SW2:创建vlan1【交换机自带】、vlan2、vlan100、vlan3
interface GigabitEthernet0/0/1
port link-type access
port default vlan 2
interface GigabitEthernet0/0/2
port link-type access
port default vlan 3
interface GigabitEthernet0/0/12
port link-type trunk
port trunk allow-pass vlan 2 to 4094
interface GigabitEthernet0/0/23
port link-type trunk
port trunk allow-pass vlan 2 to 4094SW3:创建vlan1【交换机自带】、vlan2、vlan100、vlan4
interface GigabitEthernet0/0/1
port link-type access
port default vlan 100
interface GigabitEthernet0/0/2
port link-type access
port default vlan 4
interface GigabitEthernet0/0/13
port link-type trunk
port trunk allow-pass vlan 2 to 4094
interface GigabitEthernet0/0/23
port link-type trunk
port trunk allow-pass vlan 2 to 4094配置VRRP:SW3做主VRRP、SW2做备用VRRP
SW3:interface Vlanif1
ip address 192.168.1.250 255.255.255.0
vrrp vrid 1 virtual-ip 192.168.1.254\\配置虚拟网关IP
vrrp vrid 1 priority 150\\配置优先级
vrrp vrid 1 track interface GigabitEthernet0/0/2 reduced 100
\\配置链路跟踪使其断掉后优先级下降100
interface Vlanif2
ip address 192.168.2.250 255.255.255.0
vrrp vrid 2 virtual-ip 192.168.2.254\\配置虚拟网关IP
vrrp vrid 2 priority 150\\配置优先级
vrrp vrid 2 track interface GigabitEthernet0/0/2 reduced 100
\\配置链路跟踪使其断掉后优先级下降100
interface Vlanif100
ip address 192.168.100.253 255.255.255.0
vrrp vrid 100 virtual-ip 192.168.100.254\\配置虚拟网关IP
vrrp vrid 100 priority 150\\配置优先级
vrrp vrid 100 track interface GigabitEthernet0/0/2 reduced 100
\\配置链路跟踪使其断掉后优先级下降100
SW2:interface Vlanif1
ip address 192.168.1.253 255.255.255.0
vrrp vrid 1 virtual-ip 192.168.1.254\\配置虚拟网关IP
interface Vlanif2
ip address 192.168.2.253 255.255.255.0
vrrp vrid 2 virtual-ip 192.168.2.254\\配置虚拟网关IP
interface Vlanif100
ip address 192.168.100.250 255.255.255.0
vrrp vrid 100 virtual-ip 192.168.100.254\\配置虚拟网关IP配置OSPF:SW3:ospf 1 router-id 3.3.3.3
area 0.0.0.0
network 192.168.1.0 0.0.0.255
network 192.168.2.0 0.0.0.255
network 192.168.100.0 0.0.0.255
network 192.168.4.0 0.0.0.255
SW2:ospf 1 router-id 2.2.2.2
area 0.0.0.0
network 192.168.1.0 0.0.0.255
network 192.168.2.0 0.0.0.255
network 192.168.3.0 0.0.0.255
interface Vlanif3
ip address 192.168.3.1 255.255.255.0
interface Vlanif4
ip address 192.168.4.1 255.255.255.0配置防火墙【ASA】:interface GigabitEthernet0
nameif inside1
security-level 100
ip address 192.168.4.254 255.255.255.0
interface GigabitEthernet1
nameif inside2
security-level 100
ip address 192.168.3.254 255.255.255.0
interface GigabitEthernet2
nameif outside
security-level 0
ip address 200.8.8.1 255.255.255.252配置防火墙下一跳:
route inside1 192.168.1.0 255.255.255.0 192.168.4.1
route inside1 192.168.2.0 255.255.255.0 192.168.4.1
route inside1 192.168.100.0 255.255.255.0 192.168.4.1配置ISP:interface GigabitEthernet0/0/0
ip address 200.8.8.2 255.255.255.252 \\配置IP【子网为30位】
interface GigabitEthernet0/0/1
ip address 200.9.9.254 255.255.255.0\\配置IP
默认路由:ip route-static 0.0.0.0 0.0.0.0 200.8.8.1配置防火墙对ISP下一跳:
route outside 200.9.9.0 255.255.255.0 200.8.8.2防火墙设置ACL【使外网可访问内网的web服务】:
access-list out-to-in permit tcp host 200.9.9.2 host 192.168.100.1 eq 80调用ACL:
access-group out-to-in in interface outsideNAT地址转换【将私有地址转换为公有地址119.1.1.0/29】:
object network vlan1\\配置vlan1 NAT
subnet 192.168.1.0 255.255.255.0
nat (inside1,outside) dynamic 119.1.1.1
quit
object network vlan2\\配置vlan2 NAT
subnet 192.168.2.0 255.255.255.0
nat (inside1,outside) dynamic 119.1.1.2
quit
object network vlan100 \\配置vlan100 NAT
subnet 192.168.100.0 255.255.255.0
nat (inside1,outside) dynamic 119.1.1.3
quit客户端IP:
Client1:192.168.1.1 255.255.255.0
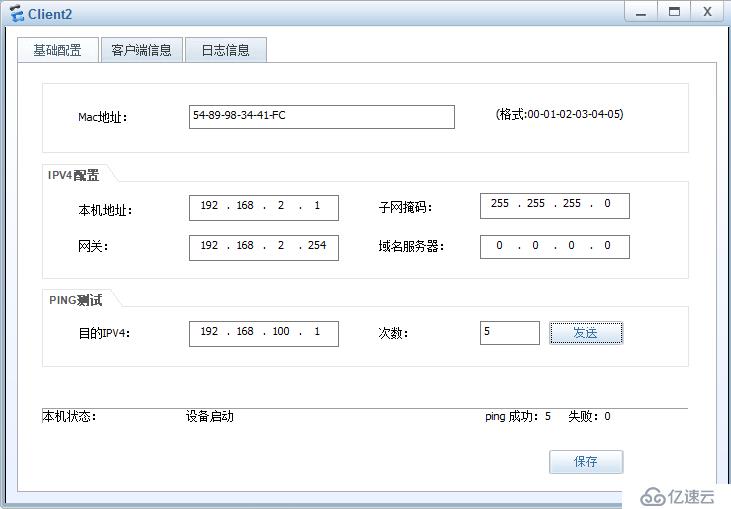
Client2:192.168.2.1 255.255.255.0
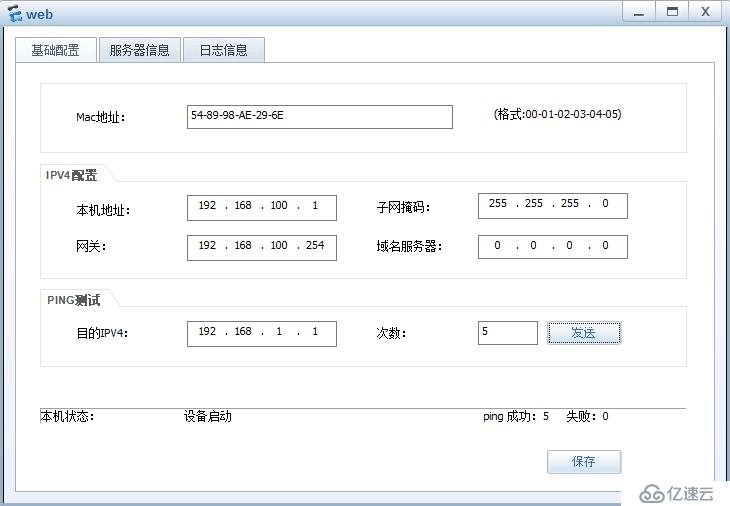
Server-web:192.168.100.1 255.255.255.0
Client3:200.9.9.2 255.255.255.0
Server-ftp:200.9.9.1 255.255.255.0结果验证:
1vlan互通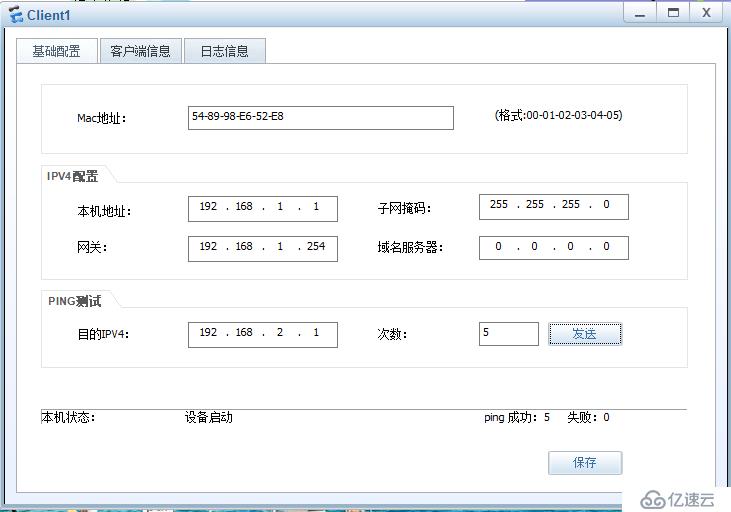
2VRRP【此时ping的为虚拟网关IP】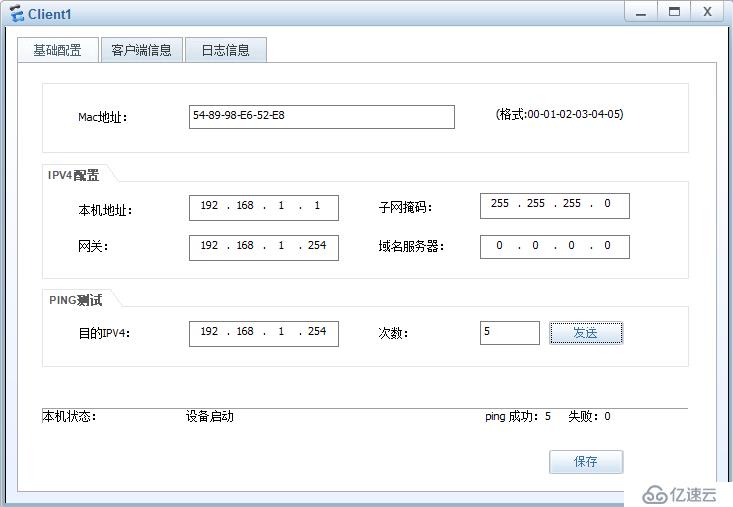
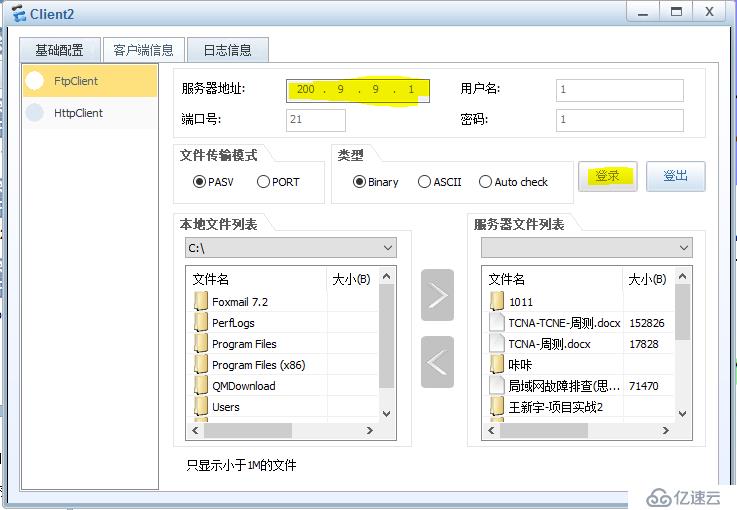
3内网PAT访问外网【地址将转换成119.1.1.0/29的网段】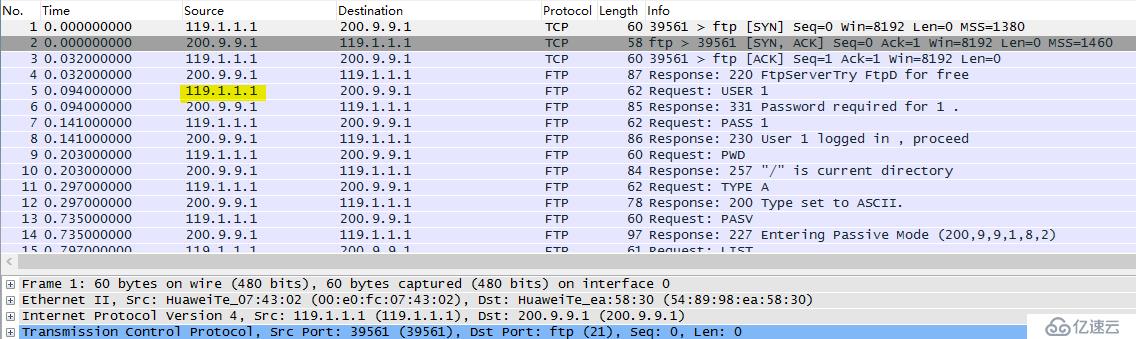

4发布Web服务器供外网访问【Client3为外网客户端】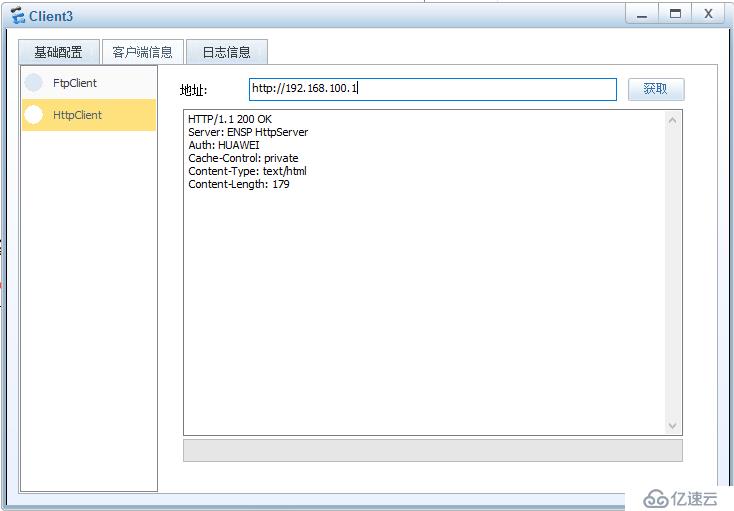
实验拓扑图【红点代表信号不稳定,不是未开启,数据可以通过】: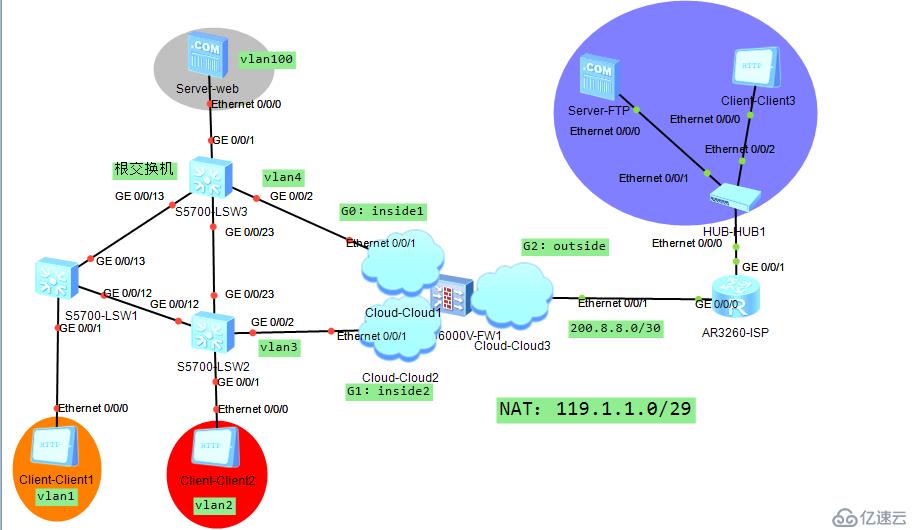
谢谢大家支持
免责声明:本站发布的内容(图片、视频和文字)以原创、转载和分享为主,文章观点不代表本网站立场,如果涉及侵权请联系站长邮箱:is@yisu.com进行举报,并提供相关证据,一经查实,将立刻删除涉嫌侵权内容。