您好,登录后才能下订单哦!
很多地方看见对SVTI的说明是gre over ipsec,因为这个东西都加密了,看不见内容,也说不了什么。
偶然看见思科社区http://www.cisco-club.com.cn/space-113351-do-blog-id-8866.html关于juniper SRX和思科对联SVTI,具体看了一下juniper配置,完全是ipsec的接口模式,没有gre参与,想来是一些人看见配置是tunnel就以为还是gre的东西,能喝SRX对接成功的肯定使用的是相同的技术,不会用gre。想验证一下,但是加密内容不可视,想来想去,可以看包大小是否一致,就能看出是不是一样。
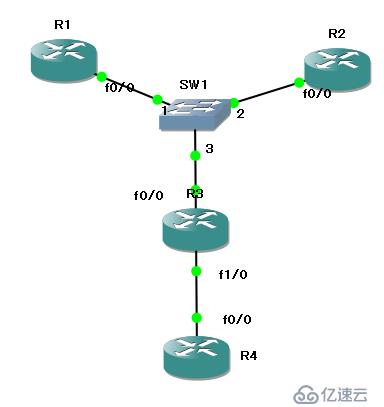
试验,在R1上配SVTI,R2上配传统的crypto map,R4两个都配。
R1
crypto isakmp policy 10
authentication pre-share
crypto isakmp key cisco address 40.1.1.2
!
!
crypto ipsec transform-set ESP-des-md5 esp-des esp-md5-hmac
!
crypto ipsec profile ipsec-profile
set transform-set ESP-des-md5
!
!
!
!
!
interface Loopback0
ip address 1.1.1.1 255.255.255.255
!
interface Tunnel0
ip address 172.16.1.1 255.255.255.0
tunnel source 61.1.1.1
tunnel destination 40.1.1.2
tunnel mode ipsec ipv4
tunnel protection ipsec profile ipsec-profile
!
interface FastEthernet0/0
ip address 61.1.1.1 255.255.255.0
duplex auto
speed auto
!
no ip http server
no ip http secure-server
ip route 0.0.0.0 0.0.0.0 61.1.1.3
ip route 1.1.1.4 255.255.255.255 Tunnel0
R2
crypto isakmp policy 10
authentication pre-share
crypto isakmp key cisco address 40.1.1.2
!
!
crypto ipsec transform-set ESP-des-md5 esp-des esp-md5-hmac
!
crypto map mm 10 ipsec-isakmp
set peer 40.1.1.2
set transform-set ESP-des-md5
match address 100
!
!
!
!
interface Loopback0
ip address 1.1.1.2 255.255.255.255
!
interface FastEthernet0/0
ip address 61.1.1.2 255.255.255.0
duplex auto
speed auto
crypto map mm
!
no ip http server
no ip http secure-server
ip route 0.0.0.0 0.0.0.0 61.1.1.3
!
!
!
access-list 100 permit ip host 1.1.1.2 host 1.1.1.4
R4
crypto isakmp policy 10
authentication pre-share
crypto isakmp key cisco address 61.1.1.1
crypto isakmp key cisco address 61.1.1.2
!
!
crypto ipsec transform-set ESP-des-md5 esp-des esp-md5-hmac
!
crypto ipsec profile ipsec-profile
set transform-set ESP-des-md5
!
!
crypto map mm 10 ipsec-isakmp
set peer 61.1.1.2
set transform-set ESP-des-md5
match address 100
!
!
!
!
interface Loopback0
ip address 1.1.1.4 255.255.255.255
!
interface Tunnel0
ip address 172.16.1.4 255.255.255.0
tunnel source 40.1.1.2
tunnel destination 61.1.1.1
tunnel mode ipsec ipv4
tunnel protection ipsec profile ipsec-profile
!
interface FastEthernet0/0
ip address 40.1.1.2 255.255.255.0
duplex auto
speed auto
crypto map mm
!
no ip http server
no ip http secure-server
ip route 0.0.0.0 0.0.0.0 40.1.1.1
ip route 1.1.1.1 255.255.255.255 Tunnel0
!
!
!
access-list 100 permit ip host 1.1.1.4 host 1.1.1.2
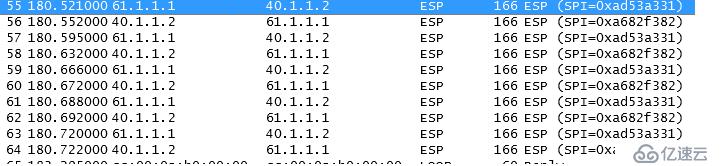
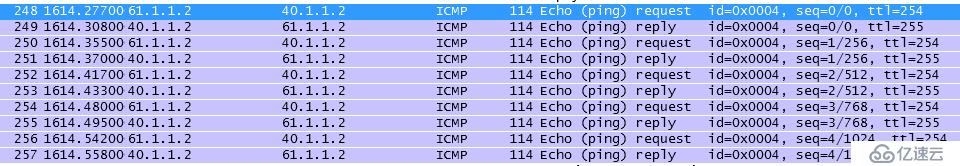
从R1和R2分别ping R4,通过抓包,比较ESP包大小,完全一样,其后又用telnet试验,发现包的大小仍然一致,SVTI的包和原来的IPsec没有不同,不是所谓的gre over ipsec。
参看思科网站http://www.cisco.com/en/US/docs/ios-xml/ios/sec_conn_***ips/configuration/15-s/sec-ipsec-virt-tunnl.html
SVTI configurations can be used for site-to-site connectivity in which a tunnel provides always-on access between two sites. The advantage of using SVTIs as opposed to crypto map configurations is that users can enable dynamic routing protocols on the tunnel interface without the extra 24 bytes required for GRE headers, thus reducing the bandwidth for sending encrypted data.
人家没说过封装gre,只是进行对比,可以过动态路由并且没有gre的24字节的包头。
下面的图是抓包内容。
这个是原始ipsec站点的ping包封装成ESP
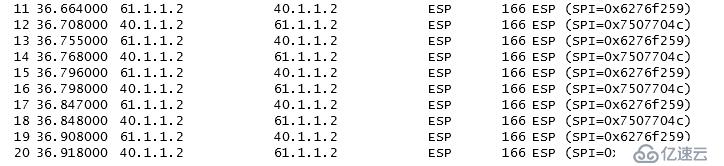
这个是SVTI的,和上面的比,size都是166
这个是 gre over ipsec的,size大了24,和思科网站上说非常吻合。

这个是一般的icmp包,ipsec之后增加52字节。可见加密还是很消耗有效载荷的。
免责声明:本站发布的内容(图片、视频和文字)以原创、转载和分享为主,文章观点不代表本网站立场,如果涉及侵权请联系站长邮箱:is@yisu.com进行举报,并提供相关证据,一经查实,将立刻删除涉嫌侵权内容。